Hardware-driven network monitoring for MSPs and enterprises

Software tools have become the default for network monitoring, but they can't capture everything. For MSPs managing dozens of client sites and enterprises with distributed infrastructure, software-only approaches frequently leave gaps at network edges, struggle under high-throughput conditions, and miss critical traffic events entirely. This guide covers the specific hardware components, such as TAPs, Network Packet Brokers (NPBs), and SmartNICs, that address these limitations, and explains how to integrate them into scalable, hybrid monitoring architectures that give you complete, reliable visibility across every location you manage.
Table of Contents
- Why hardware matters: Addressing blind spots and scalability
- Key hardware types: TAPs, NPBs, and SmartNICs explained
- Deploying hardware for real-world visibility: Scalable architectures
- Hybrid and hardware-accelerated monitoring: Integrating software and hardware
- Why software-only monitoring limits your visibility (and what works instead)
- Take your network monitoring further with Netverge hardware solutions
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Hardware closes visibility gaps | Integrating hardware TAPs and NPBs prevents blind spots and offers lossless data capture. |
| SmartNICs boost precision | SmartNICs enable ultra-low latency monitoring and programmable telemetry for demanding networks. |
| Hybrid architectures scale efficiently | Combining hardware and software lets you optimize performance, utilization, and rapid threat response. |
| Deployment strategies matter | Proper placement and type selection of hardware ensures scalable monitoring, especially across multiple locations. |
| Future-proof with advanced hardware | AI-driven and ruggedized hardware solutions address growing network complexity and environments. |
Why hardware matters: Addressing blind spots and scalability
Software monitoring tools are powerful, but they operate with a fundamental constraint: they depend on data being forwarded to them. At network edges, high-traffic segments, and locations with intermittent connectivity, this creates blind spots. Packets get dropped. Sampling introduces error. Events that matter go undetected.
Hardware monitoring components solve this by sitting in the data path, capturing traffic directly and with precision. This isn't a minor operational difference. It changes what you can actually see.
"For MSPs and multi-location enterprises, hardware integration via NPBs and TAPs at edges reduces blind spots, optimizes tool utilization (e.g., 50% CAPEX savings via aggregation), and supports scalable visibility without production impact."
For MSPs operating across multiple client networks, the scalability argument is especially strong. A single software platform may handle polling and alerting effectively, but when throughput climbs into the multi-gigabit range at even one site, visibility gaps appear fast. Hardware TAPs (Test Access Points) intercept traffic at the physical layer without disrupting the live network. NPBs aggregate, filter, and forward that traffic to monitoring tools, reducing the volume each tool must handle and preventing overload.
The impact on smarter network monitoring outcomes is direct. Teams that integrate hardware components alongside their software platforms report fewer missed events, faster anomaly detection, and more reliable data for forensic analysis.
Key reasons hardware matters for MSPs and enterprises:
- Lossless capture: Hardware TAPs capture every packet without dropping, regardless of traffic volume.
- Reduced tool sprawl: NPBs aggregate feeds from multiple network segments, so each monitoring tool receives only relevant, filtered traffic.
- No production impact: Passive TAPs create a copy of traffic without touching the live flow.
- Edge coverage: Hardware placed at remote sites extends visibility to locations where software agents may be unreliable.
- Scalability: Hardware handles throughput spikes that would overwhelm software-based capture agents.
For decision-makers evaluating network monitoring strategies, hardware integration represents a structural upgrade, not just an additional tool layer.
Key hardware types: TAPs, NPBs, and SmartNICs explained
Understanding why hardware matters leads to the next question: Which types of hardware are most important to modern network monitoring?
There are three primary hardware categories to know: TAPs, NPBs, and SmartNICs. Each serves a distinct function and fits specific deployment contexts.
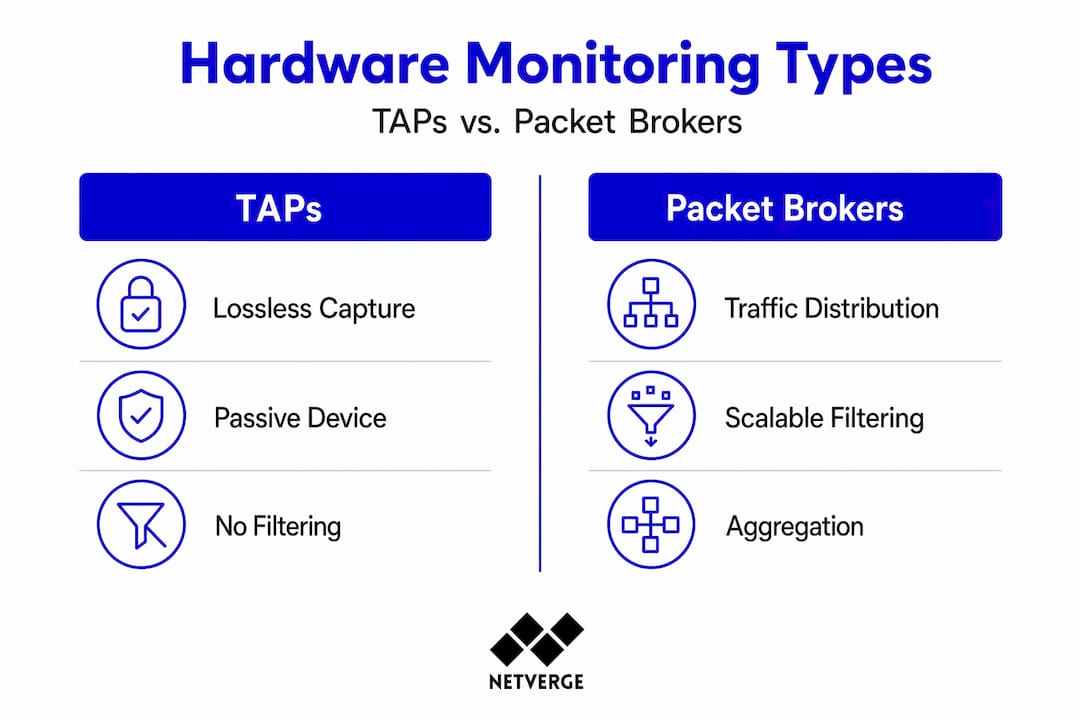
TAPs and packet brokers
TAPs are passive devices installed directly in the network path. They create an exact copy of all traffic passing through a link and forward that copy to monitoring tools. Because they operate at the physical layer, they introduce no latency to the live network and cannot be bypassed by attackers.

Hardware TAPs and Packet Brokers enable zero packet loss capture in aggregation, regeneration, and bypass modes, with up to 500 filters for targeted traffic selection, making them ideal for multi-location deployments.
NPBs extend this capability. Where a TAP captures everything, an NPB decides where that traffic goes and in what form. NPBs can filter by protocol, port, IP range, or VLAN. They can aggregate feeds from multiple TAPs, de-duplicate packets, strip headers, and distribute traffic to different monitoring tools based on policy. This prevents any single tool from being overwhelmed by raw, unfiltered data.
SmartNICs
SmartNICs (Smart Network Interface Cards) are programmable NICs that offload packet processing from the host CPU. In monitoring environments, they enable precise telemetry collection, timestamping, and filtering directly at the hardware level, before traffic ever reaches the operating system stack.
FPGA-based SmartNICs and platforms provide Layer 1+ features including port mirroring, tapping, packet stats, precise timestamping, and ultra-low latency (5ns) for high-precision monitoring. At 5 nanosecond precision, timestamping accuracy at this level is critical for detecting microbursts and correlating events across distributed nodes.
Hardware comparison
| Hardware type | Primary function | Best use case | Packet loss risk | Latency impact |
|---|---|---|---|---|
| Passive TAP | Copy traffic at the physical layer | Full packet capture at critical links | None | None |
| Network Packet Broker | Aggregate, filter, distribute traffic | Multi-tool environments, high-throughput sites | None | Minimal |
| SmartNIC | Offload processing, collect telemetry | High-frequency, low-latency environments | None | Ultra-low (5ns) |
Gigamon GigaVUE HC Series NPBs scale to 25Tbps across 32 nodes, supporting inline and out-of-band monitoring, Flow Mapping for any-to-any traffic distribution, and minimizing tool overload. That scale is relevant for large enterprises and MSPs managing dozens of high-throughput sites concurrently.
For complete network visibility, combining TAPs at critical links with an NPB for traffic distribution gives you structured, filtered, lossless data flowing to every monitoring tool in your stack.
Pro Tip: When selecting hardware for high-frequency environments, prioritize devices with hardware timestamping and programmable filters. These capabilities let you correlate events precisely across sites and isolate traffic patterns without overloading your analysis tools.
You can explore network observability hardware options designed specifically for MSP and enterprise deployments.
Deploying hardware for real-world visibility: Scalable architectures
Now that you know your hardware options, let's look at how these devices fit into real-world multi-site and MSP network architectures.
Deployment is where hardware decisions translate into actual visibility. The placement of TAPs and NPBs determines what you see and what you miss. A TAP installed at the WAN edge of each branch captures traffic entering and leaving the site. An NPB at a regional aggregation point consolidates feeds from multiple branches and distributes filtered traffic to centralized monitoring tools.
Recommended deployment sequence
- Identify critical monitoring points: Start with WAN uplinks, data center interconnects, and any segment carrying sensitive or high-volume traffic.
- Install passive TAPs at each point: Ensure full capture without affecting production traffic.
- Connect TAPs to a regional NPB: This consolidates feeds and reduces the number of tool connections required.
- Configure NPB filtering policies: Define traffic of interest by protocol, IP range, or application, and route it to the appropriate monitoring tools.
- Layer in SmartNICs at high-throughput nodes: For sites running 100G+ links, offload telemetry collection to SmartNICs to protect host CPU resources.
- Validate coverage: Run regular audits to confirm every critical segment has an active capture point.
Gigamon GigaVUE HC Series NPBs scale to 25Tbps across 32 nodes, supporting inline and out-of-band monitoring with Flow Mapping for any-to-any traffic distribution, which is especially valuable when you're consolidating feeds from geographically spread sites.
Multi-site and MSP architecture considerations
| Architecture type | Hardware placement | Best for |
|---|---|---|
| Centralized monitoring | NPB at core, TAPs at all edges | Enterprises with strong WAN links |
| Distributed monitoring | NPB per region, local TAPs per site | MSPs with geographically diverse clients |
| Hybrid aggregation | Regional NPBs feeding a central hub | Large MSPs with tiered client categories |
For high-availability (HA) setups, hardware monitoring can conflict with redundancy configurations. In HA environments, hardware monitoring may conflict with redundancy such as with gateway clustering, and ruggedized edge hardware handles harsh multi-site environments. Review your failover configurations before inserting TAPs inline at HA-protected links. Passive TAPs are the safer default.
Pro Tip: For remote sites exposed to temperature extremes, dust, or power instability, invest in ruggedized edge hardware. Standard rack hardware fails in these environments, and a failed TAP is a blind spot you won't know about until something goes wrong.
Pair hardware deployment with solid deployment strategies and use a dedicated real-time monitoring guide to validate your approach at each stage. For MSPs, reviewing purpose-built MSP network monitoring frameworks helps align hardware rollout with service delivery requirements.
Hybrid and hardware-accelerated monitoring: Integrating software and hardware
Building on deployment strategies, let's explore how hardware and software can be combined for optimal network monitoring.
Software monitoring tools excel at polling-based data collection, dashboard aggregation, alerting, and analytics. They are flexible, easy to update, and capable of correlating data across many sources. But they hit a ceiling at scale. High-throughput environments expose their sampling limitations, and CPU-bound packet capture degrades under load.
Hardware fills this gap by handling the work that software can't perform efficiently at scale. SmartNICs offload packet inspection and telemetry from the host CPU. NPBs filter and deduplicate before data reaches software tools. Hardware timestamping ensures accuracy that software clocks simply can't match.
Hardware offloads like NP acceleration alter packet flows for optimized processing, while SmartNICs enable programmable offloads for telemetry and PTP (Precision Time Protocol) synchronization. This matters because accurate time correlation across distributed nodes is a prerequisite for precise anomaly detection and forensic analysis.
The real-world impact of hardware acceleration is measurable. The AMS-IX case study achieved a 45-second DDoS mitigation using hardware-accelerated flow monitoring, and the AI inference hardware market for NICs is projected to reach $77 billion by 2030, reflecting growing industry demand for hardware-assisted network intelligence.
Key benefits of the hybrid hardware-software architecture:
- CPU efficiency: SmartNICs offload packet processing, freeing host resources for analytics and alerting.
- Scalability without sampling: Hardware handles full line-rate capture regardless of throughput.
- Accurate telemetry: Hardware timestamps eliminate clock drift errors common in software-only environments.
- Faster threat response: Hardware-accelerated flow monitoring detects and mitigates volumetric attacks in seconds rather than minutes.
- Future-proofing: As AI inference moves closer to the network edge, hardware-equipped infrastructures will integrate AI-driven analysis more naturally.
"Hardware excels in high-throughput, lossless scenarios (e.g., 100G+ environments), while software suits polling-based monitoring; hybrid approaches via SmartNICs offload CPU for better scale."
For teams exploring intelligent network interface benefits, SmartNICs represent the clearest path toward hardware-software integration without requiring a full infrastructure overhaul. And for organizations ready to add AI-powered monitoring on top of their hardware layer, the combination creates a network visibility platform that scales proactively rather than reactively.
Why software-only monitoring limits your visibility (and what works instead)
Having examined hybrid approaches, let's get real about what IT leaders learn after years of managing complex networks.
Most organizations overestimate what their software monitoring stack actually covers. Dashboards look complete. Alert thresholds seem properly configured. Reports show uptime. And then a breach surfaces, or a performance degradation goes undetected for hours, or a forensic investigation turns up packet loss nobody knew was happening. The software was reporting what it could see. It wasn't seeing everything.
The uncomfortable truth is that software monitoring is inherently limited by the data it receives. If the network drops packets under load, that dropped data simply doesn't appear in your monitoring tools. If an edge site sends telemetry over an unreliable link, gaps in coverage look like normal periods. Software tools can't compensate for what they never received.
Hardware changes the equation because it captures first and routes second. A passive TAP doesn't wait for a software agent to poll. It doesn't depend on SNMP responses arriving on schedule. It captures every packet as it passes through the link, regardless of what the rest of the network is doing. This distinction matters most at exactly the moments you need visibility most: during high-load events, security incidents, and cascading failures.
The pattern we see repeatedly is that teams invest heavily in software analytics but underinvest in the data collection layer. The result is sophisticated analysis applied to incomplete data. Lossless hardware capture, precise filtering via NPBs, and scalable aggregation address this at the foundation. They don't replace software analytics. They make those analytics trustworthy.
A practical monitoring guide helps teams audit their current coverage gaps before investing in hardware. Start by identifying every network segment where traffic is either sampled or not monitored at all. Those are your hardware deployment priorities.
The organizations that build hybrid architectures, hardware for capture and aggregation, software for analysis and correlation, stop treating monitoring as a software problem with a software solution. They treat it as a data infrastructure problem that requires the right hardware foundation. The advanced sensors for visibility layer on top of that foundation to deliver the complete picture.
Take your network monitoring further with Netverge hardware solutions
The value of hardware integration is clear: lossless capture, scalable aggregation, and precise telemetry give your monitoring stack a data foundation it can actually rely on. Netverge is built to complement exactly this kind of architecture.
Netverge's network observability hardware, including Vergepoints, provides plug-and-play physical visibility designed for MSP and enterprise deployments. These hardware components feed data directly into Netverge's AI-powered platform, which correlates telemetry, detects anomalies, and triggers automated responses without requiring manual intervention. Whether you're managing a single multi-location enterprise or a portfolio of MSP clients, AI-powered monitoring solutions give your hardware data the intelligence layer it needs to drive real outcomes. If you operate as a managed service provider, explore MSP network monitoring solutions tailored to your scale and service delivery model.
Frequently asked questions
How does hardware packet capture differ from software monitoring?
Hardware offers lossless data capture at scale, while software monitoring may drop packets or rely on sampling, especially under heavy load.
What is the advantage of SmartNICs in network monitoring?
SmartNICs offload packet processing, enable programmable telemetry, and reduce monitoring latency, with ultra-low latency features such as 5ns timestamping for high-frequency networks.
How do hardware NPBs improve scalability for multi-location enterprises?
High-capacity NPBs such as those that scale to 25Tbps aggregate and filter vast traffic volumes, distributing data to tools efficiently and minimizing overload across distributed deployments.
What are common pitfalls when adding hardware monitoring to existing networks?
Blind spots linger if edges go unmonitored, and hardware can conflict with HA redundancy configurations. Ruggedized edge hardware addresses harsh multi-site environments where standard devices fail.
Is hardware monitoring necessary for smaller sites?
For lower-traffic sites, software may suffice, but hardware ensures lossless capture and future-proofs against scale. Hybrid SmartNIC approaches offload CPU processing and deliver benefits even at modest traffic volumes.
